Introduction
In the rapidly evolving world of cryptocurrencies, digital wallets like Tether (USDT) and TRON have become essential tools for managing assets. However, their popularity has also made them prime targets for hackers and scammers. This article explores the common methods used to steal from these wallets and provides actionable tips to safeguard your crypto investments.
How Digital Wallets Are Being Hacked
- Phishing Attacks
Phishing remains one of the most common methods for stealing crypto. Hackers create fake websites or send emails mimicking legitimate platforms like Trust Wallet or TRON. Unsuspecting users enter their private keys or seed phrases, giving hackers full access to their wallets . - Fake Wallets and Apps
Scammers develop counterfeit wallet apps that look identical to popular ones like Trust Wallet. Once installed, these apps steal private keys or redirect transactions to the hacker’s address . - Malware and Keyloggers
Malicious software can infect devices and record keystrokes, capturing sensitive information like passwords and private keys. Keyloggers are particularly dangerous as they operate silently in the background . - Exchange Hacks
Centralized exchanges are frequent targets for hackers. If your USDT or TRON is stored on an exchange, it’s vulnerable to large-scale breaches. For example, the 2024 BingX hack resulted in the theft of $44 million . - Social Engineering
Scammers use psychological manipulation to trick users into revealing their private keys or seed phrases. This can happen through fake customer support calls, social media scams, or even fake airdrops .
How to Protect Your Digital Wallet
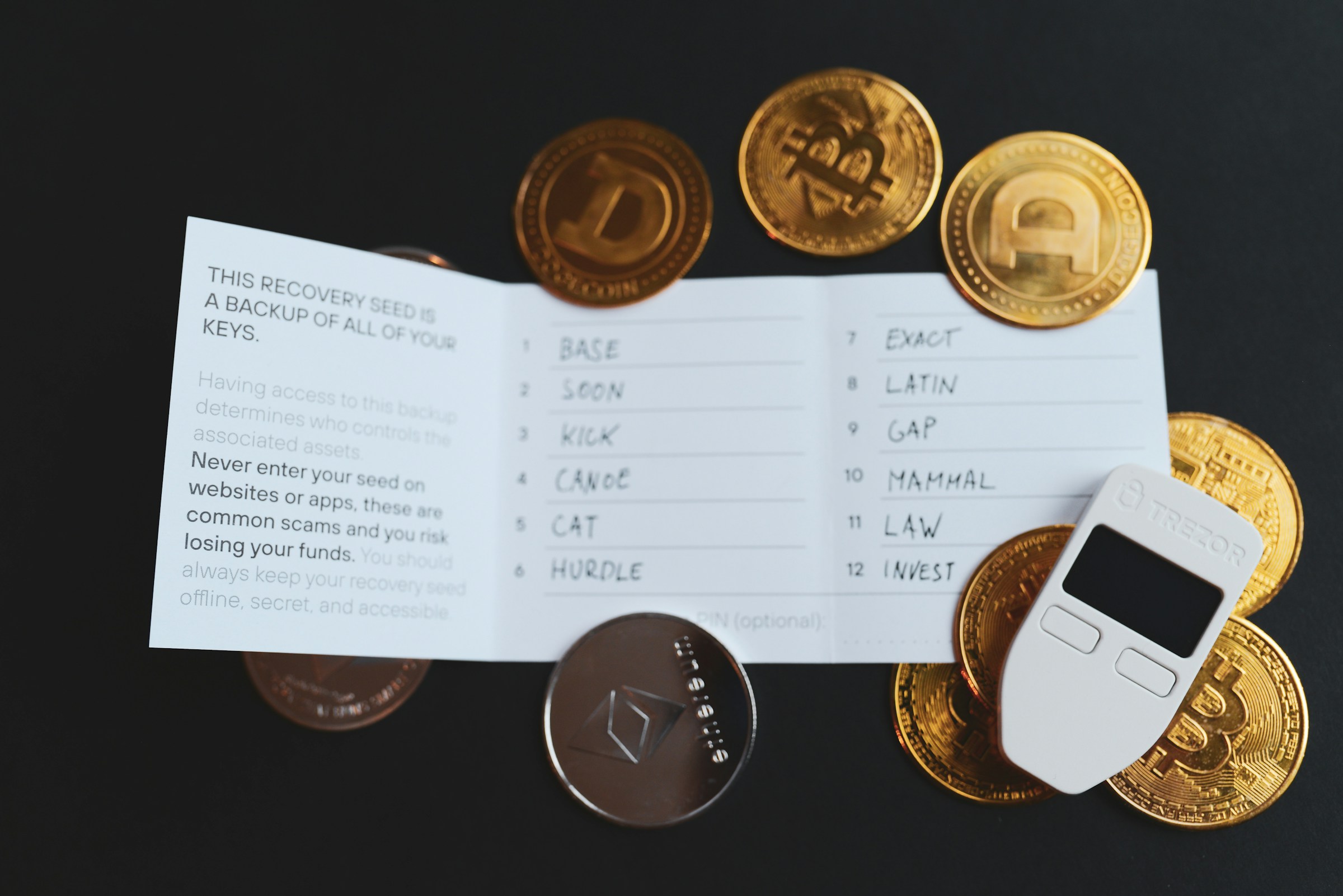
- Use Hardware Wallets
Hardware wallets like Ledger or Trezor store your private keys offline, making them immune to online attacks. They are considered the most secure way to store cryptocurrencies . - Enable Two-Factor Authentication (2FA)
Adding an extra layer of security to your accounts can prevent unauthorized access. Always enable 2FA on exchanges and wallet apps . - Verify URLs and Apps
Always double-check the URL of websites and download apps only from official sources. Avoid clicking on suspicious links in emails or social media . - Backup Your Seed Phrase Securely
Your seed phrase is the key to your wallet. Store it offline in a secure location, such as a safe or a safety deposit box. Never share it online or with anyone . - Monitor Transactions Regularly
Keep an eye on your wallet activity. If you notice unauthorized transactions, act immediately by transferring your remaining funds to a new wallet and contacting support .
What to Do If Your Wallet Is Hacked
- Change Passwords and Keys
If you suspect a breach, immediately change your passwords and generate new private keys. Move your funds to a new wallet to prevent further losses . - Contact Support
Reach out to the wallet provider or exchange for assistance. They may be able to freeze the hacker’s account or provide guidance on recovering your assets . - Report to Authorities
File a report with local law enforcement and cybercrime units. Provide all relevant transaction details to aid in the investigation . - Use Blockchain Explorers
Tools like Etherscan or Tronscan can help you track stolen funds. While recovering crypto is challenging, tracing transactions can sometimes lead to identifying the hacker .
Conclusion
The rise of digital wallets like Tether and TRON has revolutionized how we manage cryptocurrencies, but it has also introduced new risks. By understanding the methods hackers use and implementing robust security measures, you can significantly reduce the chances of falling victim to crypto theft. Stay vigilant, stay informed, and always prioritize the security of your digital assets.